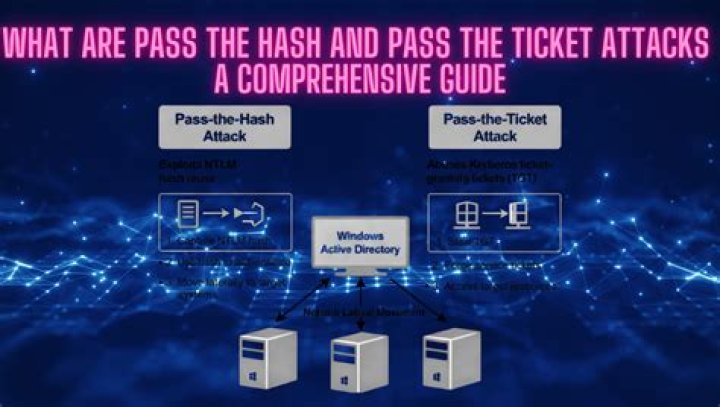
A Pass-the-Hash (PtH) attack is a technique whereby an attacker captures a password hash (as opposed to the password characters) and then simply passes it through for authentication and potentially lateral access to other networked systems. Also know, what is a pass the ticket attack?
Pass-the-Ticket attacks are a category of post-exploitation attacks involving the theft and re-use of a Kerberos ticket to authenticate to systems in a compromised environment. Once an attacker is on a system, they will attempt to elevate privileges to get access to tickets stored in other Active Directory sessions.
Similarly, which is the first step for an attacker in launching a pass the hash attack? To execute a pass the hash attack, the attacker first obtains the hashes from the targeted system using any number of hash-dumping tools. Then he or she uses a pass the hash tool to place the obtained hashes on a Local Security Authority Subsystem Service.
In this way, why does pass the hash work?
In cryptanalysis and computer security, pass the hash is a hacking technique that allows an attacker to authenticate to a remote server or service by using the underlying NTLM or LanMan hash of a user's password, instead of requiring the associated plaintext password as is normally the case.
What is Golden Ticket attack?
The Golden Ticket Attack, discovered by security researcher Benjamin Delpy, gives an attacker total and complete access to your entire domain. It's a Golden Ticket (just like in Willy Wonka) to ALL of your computers, files, folders, and most importantly Domain Controllers (DC).
Related Question Answers
What is the difference between Kerberos and LDAP?
LDAP and Kerberos together make for a great combination. Kerberos is used to manage credentials securely (authentication) while LDAP is used for holding authoritative information about the accounts, such as what they're allowed to access (authorization), the user's full name and uid. What is Kerberos authentication?
Kerberos (/ˈk?ːrb?r?s/) is a computer-network authentication protocol that works on the basis of tickets to allow nodes communicating over a non-secure network to prove their identity to one another in a secure manner. What is Kerberos attack?
During such attacks, threat actors target domain administrator privileges, which provide unrestricted access and control of the IT landscape. Armed with these privileges, attackers can stealthily manipulate Domain Controllers (and Active Directory) and generate Kerberos tickets to obtain unauthorized access. What is Silver Ticket attack?
A Silver Ticket is a forged service authentication ticket. A hacker can create a Silver Ticket by cracking a computer account password and using that to create a fake authentication ticket. In the simplest terms, a Silver Ticket is a forged authentication ticket that allows you to log into some accounts. What is an NTLM hash?
The NTLM protocol uses one or both of two hashed password values, both of which are also stored on the server (or domain controller), and which through a lack of salting are password equivalent, meaning that if you grab the hash value from the server, you can authenticate without knowing the actual password. Does AD use Kerberos?
Active Directory uses Kerberos version 5 as authentication protocol in order to provide authentication between server and client. Kerberos v5 became default authentication protocol for windows server from windows server 2003. What is Krbtgt account?
The krbtgt account acts as a service account for the Kerberos Key Distribution Center (KDC) service. The account and password are created when a domain is created and the password is typically not changed. If the krbtgt account is compromised, attackers can create valid Kerberos Ticket Granting Tickets (TGT). What is the difference between LM and NTLM passwords hashes?
The LM hash has a limited character set of only 142 characters, while the NT hash supports almost the entire Unicode character set of 65,536 characters. 3. The NT hash calculates the hash based on the entire password the user entered. The LM hash splits the password into two 7-character chunks, padding as necessary. What hashing means?
Hashing is the process of converting a given key into another value. A hash function is used to generate the new value according to a mathematical algorithm. The result of a hash function is known as a hash value or simply, a hash. What is a hash value?
A hash value is a numeric value of a fixed length that uniquely identifies data. Hash values represent large amounts of data as much smaller numeric values, so they are used with digital signatures. You can sign a hash value more efficiently than signing the larger value. What is a rainbow table cryptographic attack?
A rainbow table attack is a type of hacking wherein the perpetrator tries to use a rainbow hash table to crack the passwords stored in a database system. A rainbow table is a hash function used in cryptography for storing important data such as passwords in a database. What are hashes used for in security?
Hashing is an algorithm performed on data such as a file or message to produce a number called a hash (sometimes called a checksum). The hash is used to verify that data is not modified, tampered with, or corrupted. In other words, you can verify the data has maintained integrity. What hash format are modern Windows login passwords stored in?
Removing the LM hash from all Windows systems stops this attack. Windows passwords will only be stored in the NT hash, which is much more difficult to crack. Which hashing algorithm do modern Windows systems use?
A: For hashing user passwords, Windows NT uses two algorithms: LM, which we have inherited from Lan Manager networks, which is based on a simple DES encryption, and NT, based upon the MD4 hashing function. Are Windows passwords salted?
While Windows doesn't currently use salting, they can encrypt stored hashes if you use the 'SYSKEY' tool. You can also use 'rounds', or hashing a password multiple times. The salt and number of rounds used is stored with the password hash, meaning that if the attacker has one, they also have the other. What is hash injection?
- A hash injection attack allow an attacker to inject a compromised hash into a local session and use the hash to validate to network resources. - The attacker finds and extracts a logged on domain admin account hash. - The attacker uses the extracted hash to lo on the domain controller. How does a collision attack work?
In cryptography, a collision attack on a cryptographic hash tries to find two inputs producing the same hash value, i.e. a hash collision. This is in contrast to a preimage attack where a specific target hash value is specified. Collision attack. Find two different messages m1 and m2 such that hash(m1) = hash(m2). What is replay attack networking?
A replay attack occurs when a cybercriminal eavesdrops on a secure network communication, intercepts it, and then fraudulently delays or resends it to misdirect the receiver into doing what the hacker wants. What is NTLM authentication protocol?
Windows Challenge/Response (NTLM) is the authentication protocol used on networks that include systems running the Windows operating system and on stand-alone systems. NTLM uses an encrypted challenge/response protocol to authenticate a user without sending the user's password over the wire. What is Mimikatz tool?
Mimikatz is an open-source application that allows users to view and save authentication credentials like Kerberos tickets. Benjamin Delpy continues to lead Mimikatz developments, so the toolset works with the current release of Windows and includes the most up-to-date attacks. How does Golden Ticket attack work?
A Golden Ticket attack is a type of attack in which an adversary gains control over an Active Directory Key Distribution Service Account (KRBTGT), and uses that account to forge valid Kerberos Ticket Granting Tickets (TGTs). How many golden tickets are there?
Five Golden Tickets
What is Golden Ticket and silver ticket?
While a Golden ticket is a forged TGT valid for gaining access to any Kerberos service, the silver ticket is a forged TGS. This means the Silver Ticket scope is limited to whatever service is targeted on a specific server. Where is Kerberos used?
Although Kerberos is found everywhere in the digital world, it is employed heavily on secure systems that depend on reliable auditing and authentication features. Kerberos is used in Posix authentication, and Active Directory, NFS, and Samba. It's also an alternative authentication system to SSH, POP, and SMTP. What does the golden ticket represent?
Like the chocolate factory, the golden ticket is a physical manifestation of the difference between poverty and wealth. Finding the golden ticket allows Charlie to live his dream. As its name indicates, the golden ticket is made entirely of gold. It is the most valuable thing Charlie has ever touched. What is Krbtgt account used for?
The KRBTGT account is used to encrypt and sign all Kerberos tickets within a domain, and domain controllers use the account password to decrypt Kerberos tickets for validation. This account password never changes, and the account name is the same in every domain, so it is a well-known target for attackers. What is the Ntds DIT file?
The Ntds. dit file is a database that stores Active Directory data, including information about user objects, groups, and group membership. It includes the password hashes for all users in the domain. Can I delete Krbtgt account?
The KRBTGT account is a local default account that acts as a service account for the Key Distribution Center (KDC) service. This account cannot be deleted, and the account name cannot be changed.